Categories
Mar 2, 2026
3 min Read
Security teams today are drowning in data but starving for context. With the average enter...
Mar 2, 2026
3 min Read
Your edge security just got a direct line to your vulnerability management program.
Feb 26, 2026
4 min Read
Running scans using different SAST, DAST, IaaC, and proprietary scanners is only half of t...
vulnerability managementASPMintegrations
Feb 23, 2026
4 min Read
The "Fix everything High/Critical in 30 days" policy is a standard in the industry, but in...
Feb 21, 2026
4 min Read
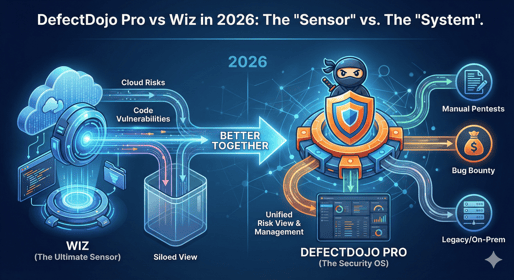
In 2026, Wiz is the "Google" of cloud security: fast, ubiquitous, and incredibly good at f...
Feb 20, 2026
5 min Read
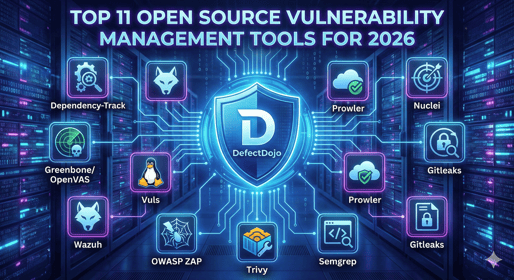
Building a top-tier open-source vulnerability management stack requires distinguishing bet...

.png?width=514&height=285&name=Gemini_Generated_Image_dsz87dsz87dsz87d%20(1).png)