Docs
The Unified Vulnerability Management Buyers Guide
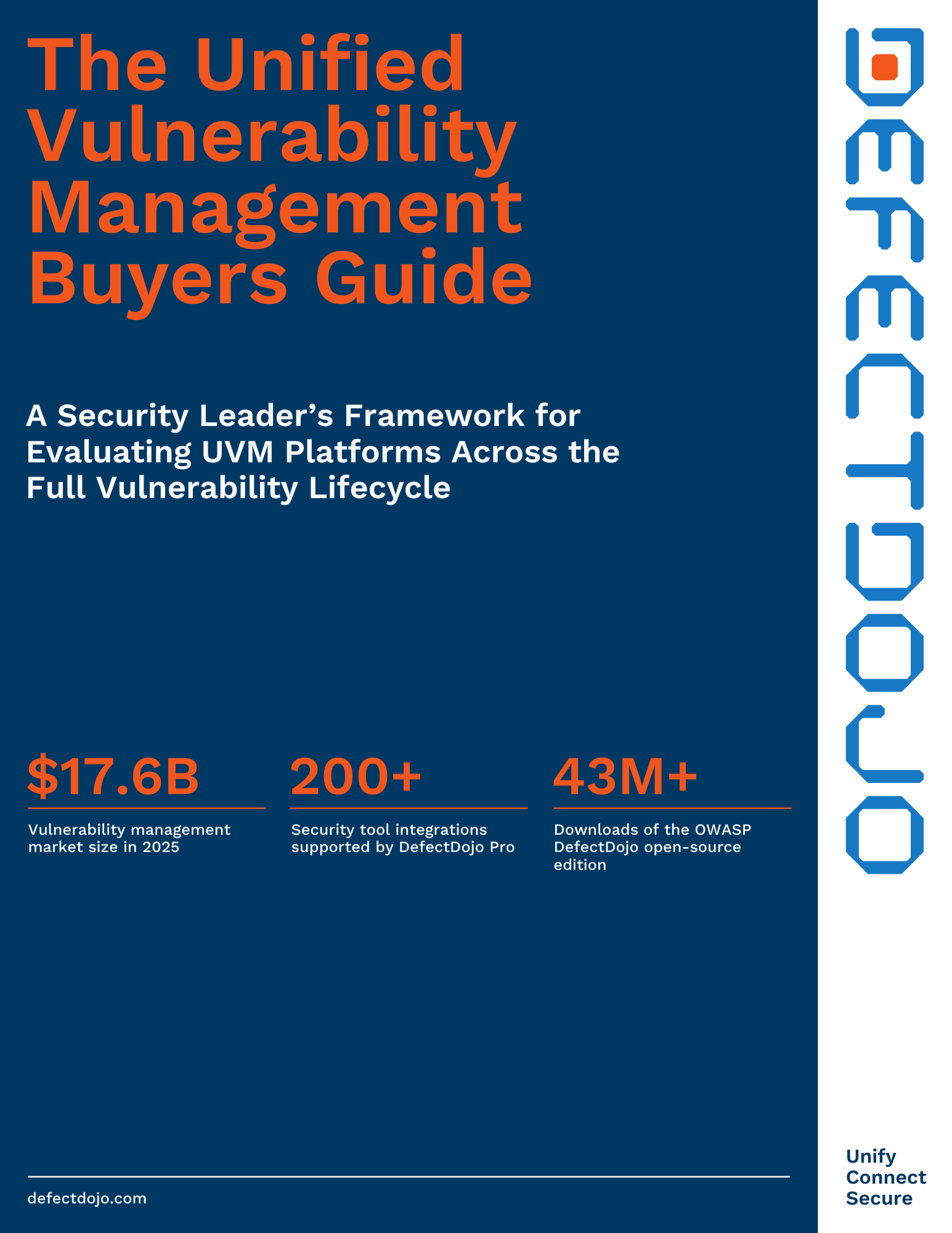
The Unified Vulnerability Management Buyers Guide gives security leaders a structured framework for consolidating fragmented scanner data into a single system of record that covers the full vulnerability lifecycle—from discovery and deduplication through SLA-driven remediation and compliance reporting. In a $17.6B market where tool sprawl and alert noise are the top barriers to effective programs, learn how to evaluate UVM platforms that unify AppSec, infrastructure, and SOC findings without locking you into a single vendor.
The Unified Vulnerability Management Buyers Guide will cover:
- The 6 vulnerability lifecycle stages every UVM platform must support—and why excelling at discovery alone isn't enough to operationalize a mature program
- The 10 must-have platform capabilities to evaluate, from intelligent cross-tool deduplication and risk-based prioritization to unified AppSec + SOC coverage and AI-ready architecture
- How to avoid the most costly purchasing pitfalls, including confusing scanning with management, per-asset pricing that punishes growth, and platforms that ignore the AppSec and infrastructure divide