Docs
The Risk-Based Vulnerability Management Buyers Guide
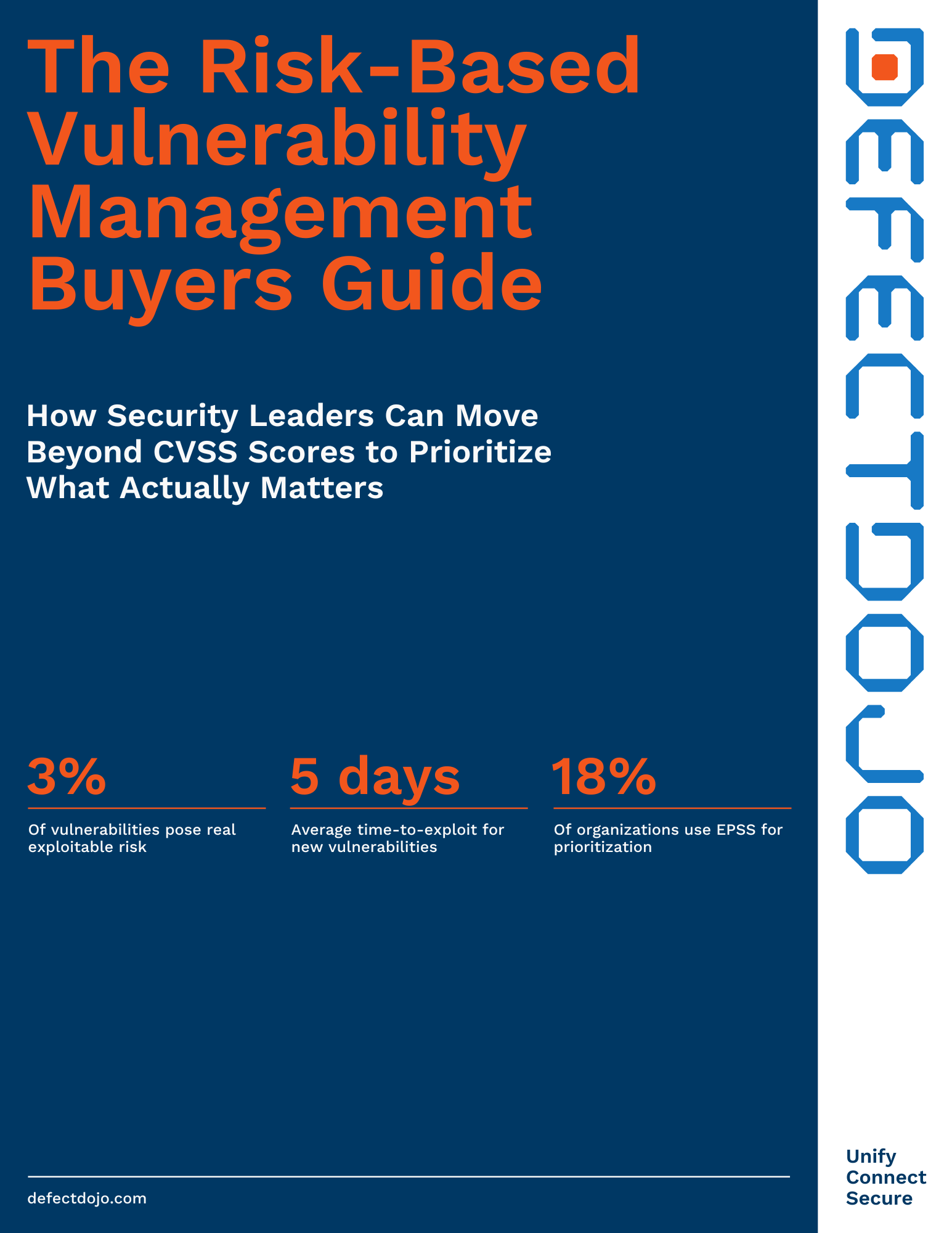
The Risk-Based Vulnerability Management Buyers Guide equips security leaders with a proven framework for moving beyond just CVSS scores to focus remediation efforts on the 3% of vulnerabilities that pose real, exploitable risk. With the average time-to-exploit now just five days, learn how to combine KEV, EPSS, and other business context to build a prioritization engine that reflects your organization's actual risk posture.
The Risk-Based Vulnerability Management Buyers Guide will cover:
- Why CVSS-only prioritization fails and which six risk inputs—including KEV status, EPSS probability, and asset criticality—drive accurate, real-world vulnerability prioritization
- The 8 must-have capabilities to evaluate in any RBVM platform, from configurable risk scoring and automated threat intel enrichment to SLA-driven remediation and lifecycle management
- How to avoid critical purchasing pitfalls like black-box risk scoring, RBVM tools without workflow integration, and per-asset pricing that penalizes program growth